how to
-

5 Alarming Truths About the Failing Economy of Cuba vs. the Economy of North Korea
Recent developments have highlighted the contrasting economic paths of Cuba and North Korea. The economy of Cuba has been gradually opening, introducing reforms that allow…
-
NIST CSF 2.0: How to Navigate Its Updates and Benefits
Cybersecurity isn’t just a buzzword—it’s an essential part of running a business in today’s digital world. Every day, new cyber threats emerge, targeting businesses of…
-
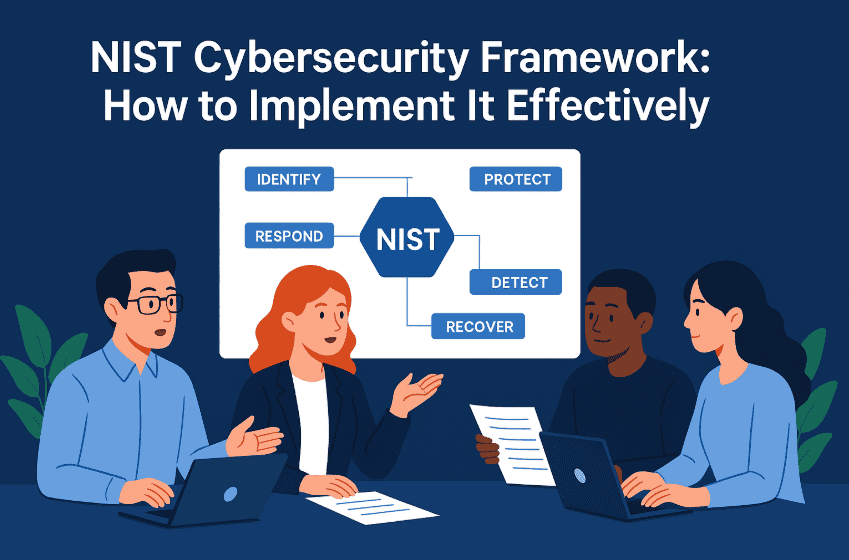
NIST Cybersecurity Framework: Implement It Effectively
Cyber threats are evolving faster than ever, making cybersecurity a top priority for businesses and individuals alike. If you’ve ever felt overwhelmed by the complexities…
-
Crypto Futures: 4 Proven Steps for Beginner Traders
Imagine having the power to trade crypto futures without actually owning it. Sounds intriguing, right? That’s exactly what crypto futures allow you to do. Whether…
-

How to Use Atomic Wallet for Cross-Chain Transactions
Cryptocurrency is evolving fast, and cross-chain transactions are the next big thing. If you’ve ever felt frustrated by swapping coins between blockchains, you’re not alone.…
-
How to Set Up a Private Cloud Storage Using OpenStack
Cloud computing has completely transformed the way businesses and developers handle data, applications, and services. It has revolutionized industries by offering scalable, flexible, and cost-efficient…
-
MCO Stock: 5 Smart Checks for Better Analysis
Investing in the stock market often feels unpredictable. The wide range of choices can make it hard to decide where to place your money, especially…
-
How to Respond to a Ransomware Attack: A Step-by-Step Guide
A Ransomware Attack can feel like the digital version of waking up to your front door wide open and your valuables missing. One minute you…
-
How to Use Crypto Staking to Maximize Rewards
Crypto staking is transforming the way investors grow their assets in the crypto market. Whether you’re a seasoned blockchain enthusiast or a beginner exploring cryptocurrencies,…
-

Endpoint Detection and Response: 10 Powerful Steps
Setting up Endpoint Detection and Response can feel a bit like installing a home security system in a house that never sleeps. Every laptop, desktop,…
