Definitions
-

Google Gemini Explained: The Powerful AI Leap Transforming How We Work
I still remember the first time I heard about Google Gemini. It came up during a late-night conversation with a friend who works in software…
-

Discover What Is Tailwind: A Powerful Shift in Web Design
If you’ve ever wondered Tailwind and why it’s all over the web development community, you’re in the right place. In the fast-evolving world of technology…
-

Mastering Snowflake: The Ultimate Cloud Data Revolution
In the ever-changing world of technology trends, few innovations have reshaped data management like Snowflake. As businesses collect massive amounts of data daily, finding efficient,…
-
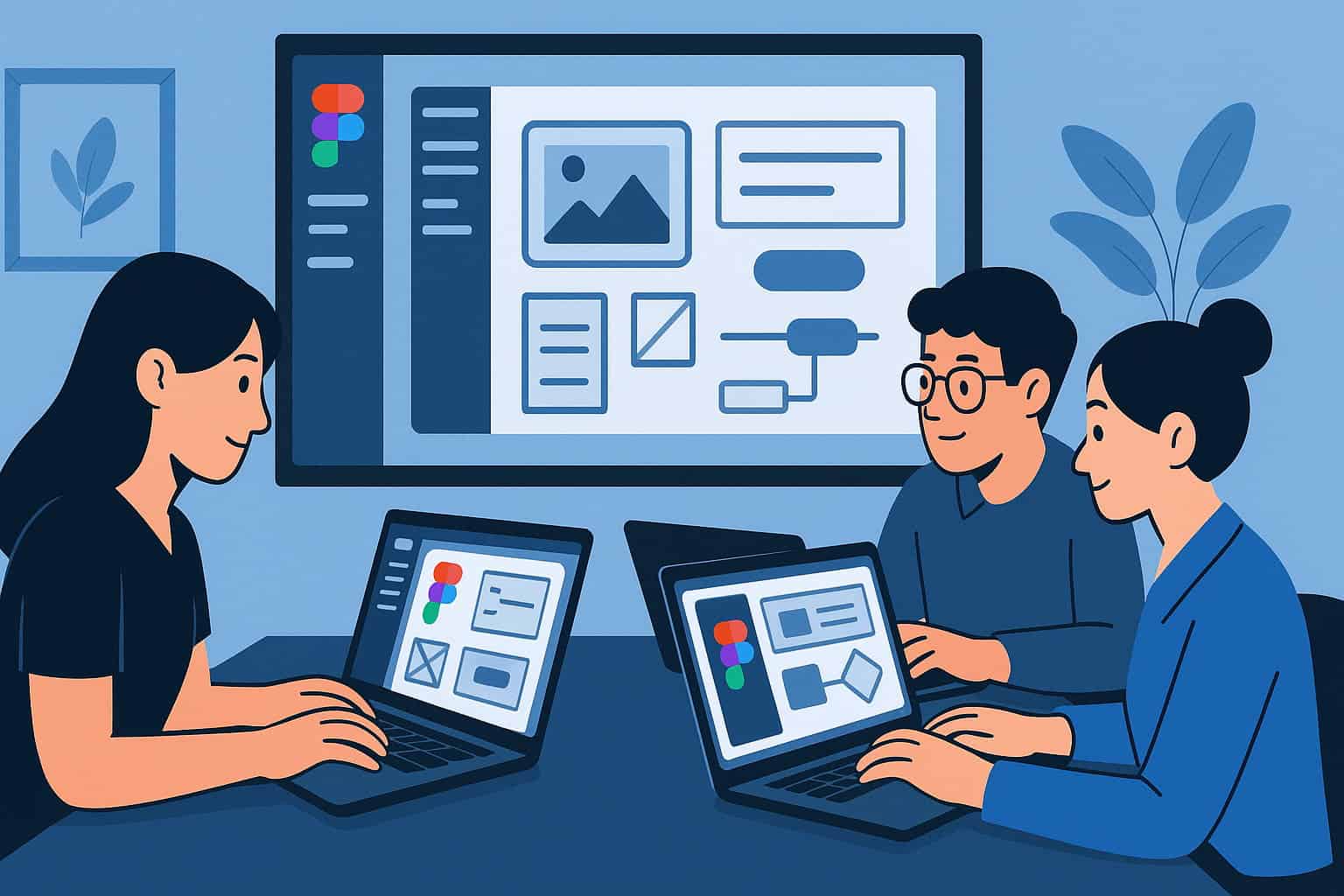
Figma Revolution: Empowering Creative Collaboration Everywhere
In today’s fast-paced world of technology trends, few tools have redefined creativity quite like Figma. This cloud-based design platform has transformed how teams create, share,…
-

The Ultimate NoSql Breakthrough for Smarter Data
NoSql is transforming the world of technology trends by changing how we store and manage data. In an age where speed, flexibility, and scalability rule,…
-
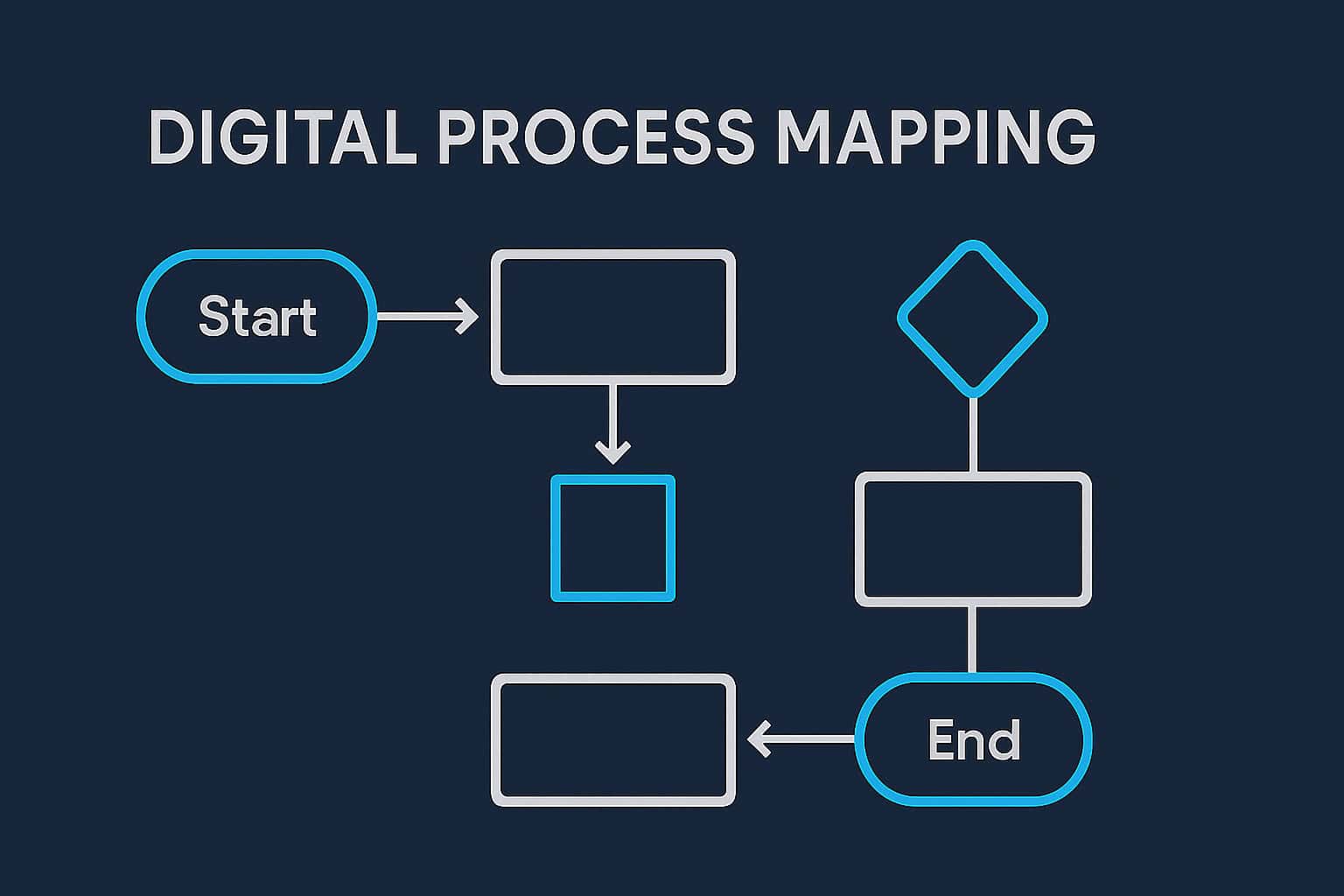
Flowchart Success: Making Technology Clear and Simple
In the ever-evolving world of technology trends, the Flowchart remains a timeless tool for clarity and innovation. Whether you’re designing a new app, streamlining business…
-

Meta Glasses Reveal the Future of Smart Vision
Imagine walking through your city, and with just a glance, your glasses show you directions, upcoming appointments, and even translate a sign in real time.…
-
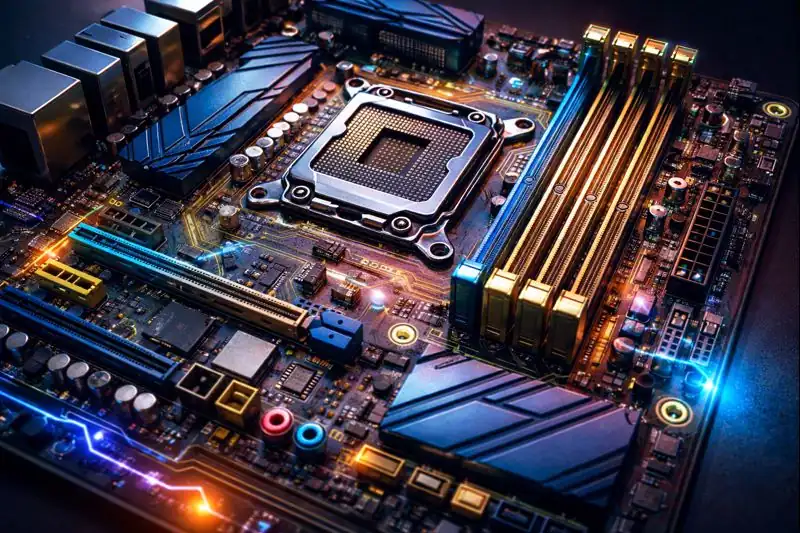
Motherboard Magic: Powering the Heart of Your PC
If you’ve ever peeked inside your computer or even thought about building one from scratch, you might have stumbled across a term that sounds more…
-

Topology Unleashed: The Secret Engine Behind Innovation
Have you ever wondered how your GPS maps out the shortest route, or how the internet connects billions of people worldwide? Beneath all these marvels…
-

Virtualization Mastery: Transforming Technology
In the ever-evolving world of Technology Trends, few innovations have reshaped the digital landscape like Virtualization. Imagine being able to run multiple computers on a…
