Definitions
-

Near Protocol: Powerful Reasons to Stay Bullish
In the fast-paced world of cryptocurrency, where innovation is constant and competition fierce, new technologies frequently emerge with bold promises. Yet few manage to deliver…
-
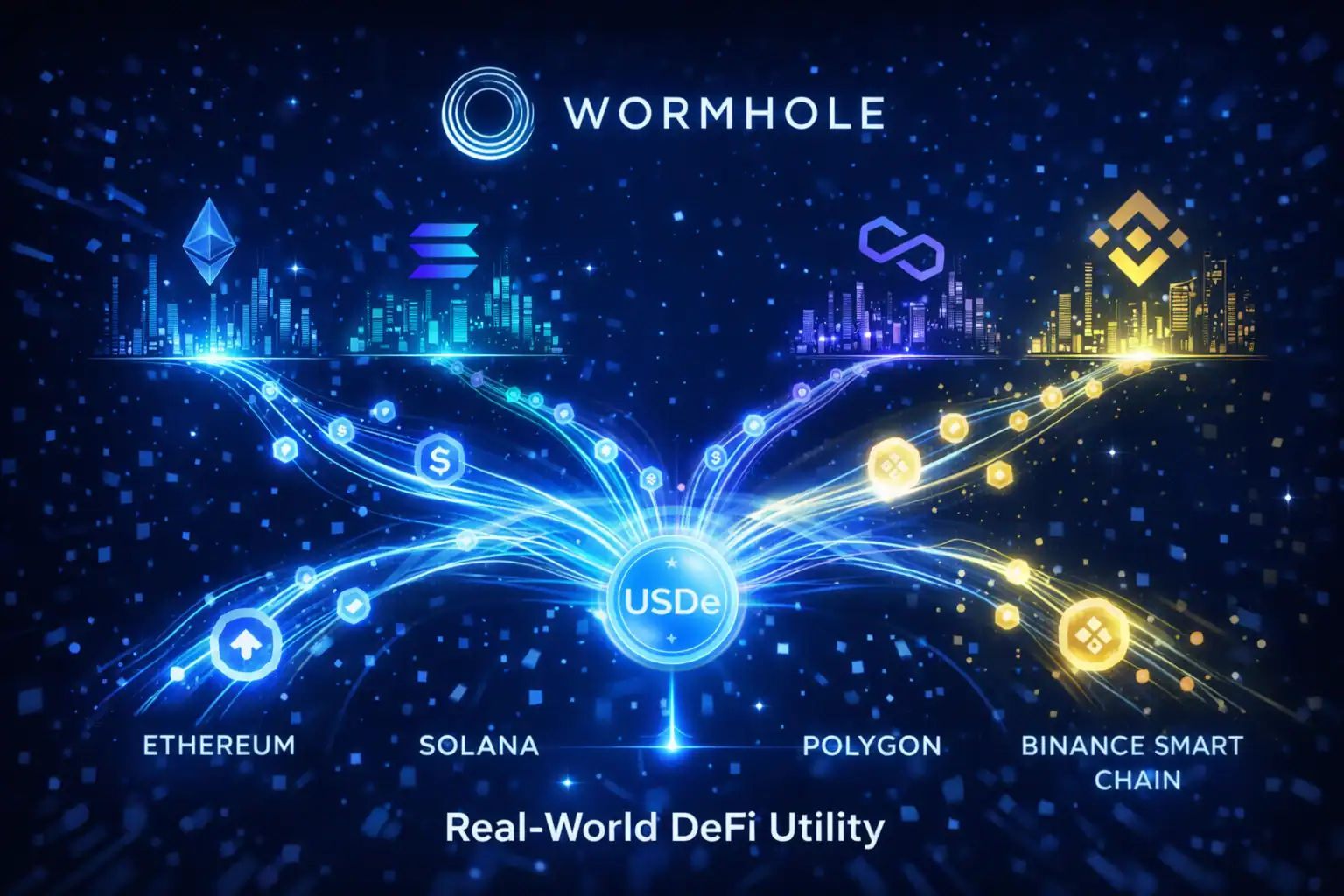
Wormhole Crypto: Powerful Guide to Cross-Chain Growth
In the fast-paced world of cryptocurrency, Wormhole Crypto is making waves for all the right reasons. As a technology that enables seamless communication between blockchains,…
-
TradingView: Economic Tools for Market Analysis
Ah, TradingView. Just hearing the name sparks images of glowing screens, pulsing charts, and buzzing trader communities. In the world of economic analysis, TradingView has…
-
TransferWise: How It Impacts Global Money Transfers and FX Rates
In today’s fast-moving world of international finance, TransferWise (now called Wise) has reshaped how people and businesses move money across borders. For anyone sending funds…
-
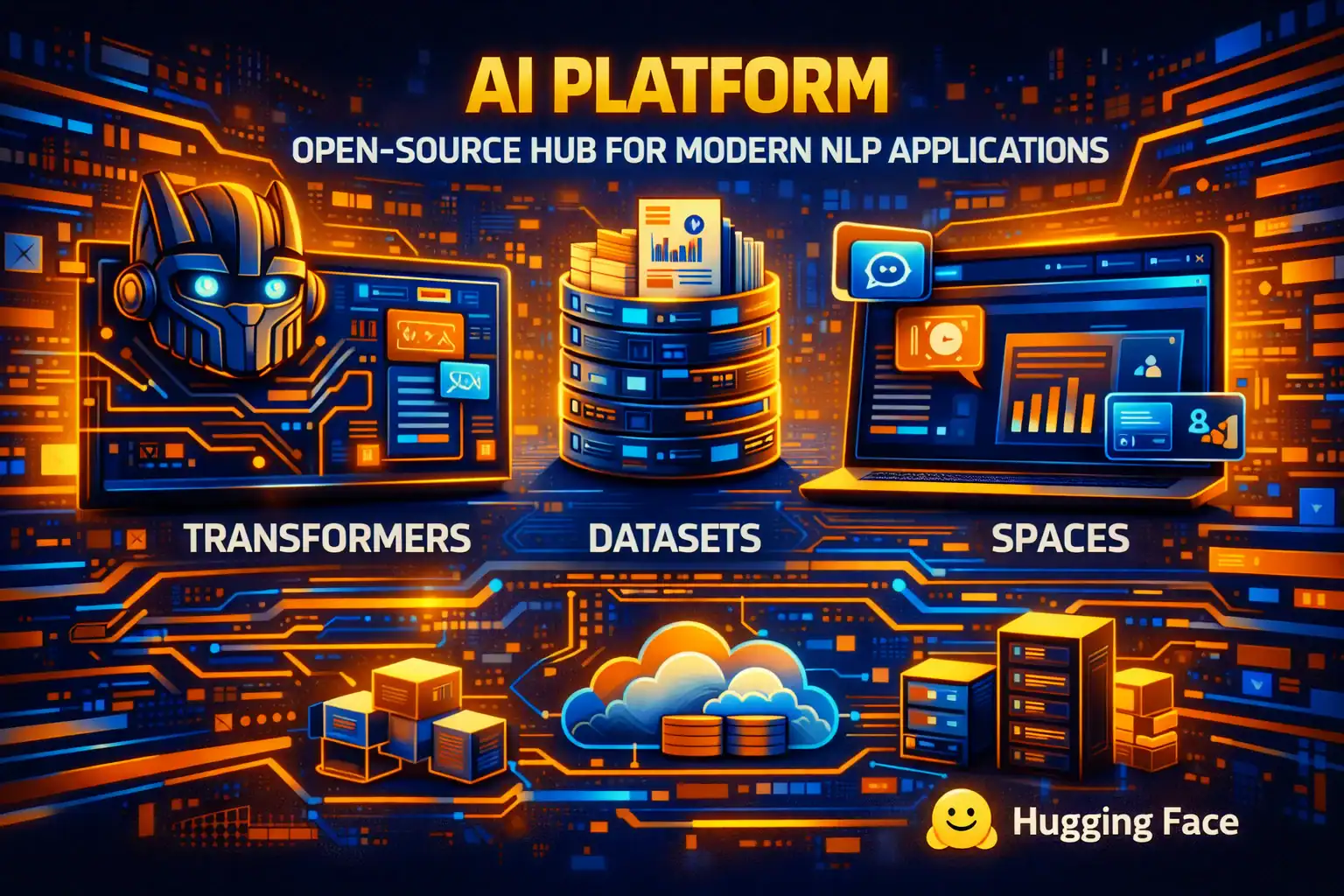
What is Hugging Face: Powerful Guide to AI Success
In today’s fast-moving Tech Trends, you’ve probably heard the term What Is Hugging Face floating around. Maybe a colleague mentioned it, or you saw it…
-

Google Vertex AI: Brilliant Power for Tomorrow’s Innovators
In today’s world of rapid digital transformation, Google Vertex AI stands out as a beacon of opportunity for businesses and individuals alike. Whether you are…
-

Understanding Side Channel Attack for Enhanced Cybersecurity
In the constantly evolving landscape of cybersecurity, side channel attack emerges as one of the most fascinating — and alarming — threats. This technique does…
-

Exciting Notcoing Wins for the Crypto Future
In the exciting world of cryptocurrency, Notcoin has sparked the attention of both gamers and investors. You might be asking, “What’s all the buzz about…
-

Claude AI: Unlocking the Power of Advanced Technology Today
Have you come across Claude AI in your reading or conversations? This fascinating tool has quickly become a talking point in the world of technology.…
-

Exploit Defense: Powerful Protection Against Cyber Risks
In today’s interconnected world, the term Exploit often surfaces in discussions about cybersecurity, but what does it truly mean? Simply put, this is a method…
