DNS spoofing, also known as DNS cache poisoning, is a sophisticated cyber threat that targets the foundation of the internet’s functionality—the Domain Name System (DNS). The DNS translates human-readable domain names, such as “example.com,” into IP addresses that computers use to communicate. When attackers manipulate this system, they can redirect users to malicious websites, intercept sensitive data, or disrupt services.
This attack is relevant in the context of cybersecurity because it exploits the trust users and devices place in the DNS. Understanding it is vital for individuals, organizations, and cybersecurity professionals to safeguard sensitive information and maintain internet integrity.
As internet usage continues to grow, DNS spoofing has become more dangerous due to the increasing number of connected devices and services. From mobile apps to cloud platforms, nearly every digital interaction relies on DNS resolution. This widespread dependency means that a single successful spoofing attack can impact thousands—or even millions—of users at once. Because of this scale, DNS spoofing is not just a technical issue but a critical business and security concern.
What is DNS Spoofing?
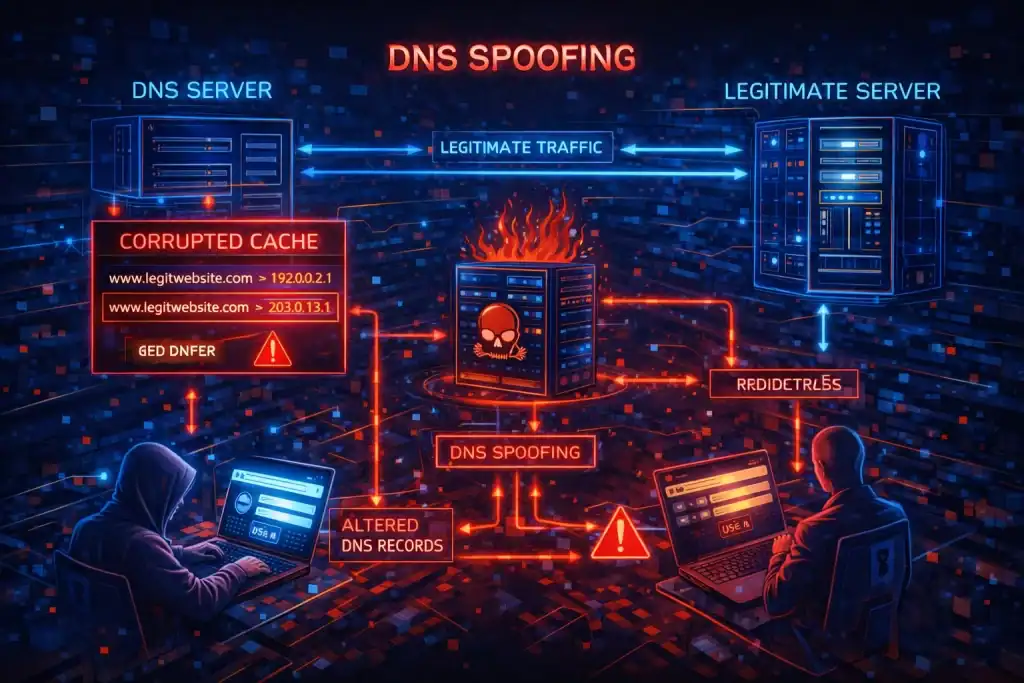
DNS spoofing is a cyberattack that involves falsifying DNS records to divert users to malicious destinations or unauthorized servers. By corrupting DNS cache data, attackers can impersonate legitimate websites, leading to phishing attacks, malware distribution, or data theft.
In simple terms, it occurs when an attacker introduces incorrect information into a DNS resolver’s cache, redirecting traffic from legitimate domains to fraudulent ones. It’s a critical concern in cybersecurity because DNS serves as the internet’s address book, and manipulating it can compromise the trust and safety of online interactions.

Synonyms for DNS spoofing include DNS cache poisoning, and DNS tampering. Each term highlights different facets of the attack but refers to the same underlying concept—manipulating DNS records for malicious purposes.
What makes DNS spoofing particularly dangerous is its invisibility to the average user. Unlike other cyberattacks that may trigger warnings or suspicious behavior, spoofed websites often look identical to legitimate ones. Users may unknowingly enter login credentials, financial details, or personal information without realizing they are interacting with a malicious system.
Additionally, DNS spoofing can bypass traditional security tools if they rely heavily on domain-based trust. Without proper validation mechanisms, systems may accept falsified DNS responses as legitimate, allowing attackers to maintain persistence within the network.
Breaking Down DNS Spoofing
DNS spoofing targets vulnerabilities in the DNS infrastructure. Here’s how the attack typically unfolds:
Reconnaissance: Attackers identify a vulnerable DNS server.
Injection: They inject forged DNS responses, convincing the server to accept and cache false information.
Redirection: Subsequent users querying the DNS server are unknowingly directed to malicious IP addresses.
For example, a user trying to visit “bank.com” may be redirected to a fake website that looks identical to the original but is designed to steal login credentials. Such attacks can target individuals or organizations, with implications ranging from personal data breaches to widespread service disruptions.
Attackers often enhance these techniques by exploiting weak DNS configurations, predictable transaction IDs, or unsecured network traffic. In some cases, they may combine DNS spoofing with other attack methods such as phishing or malware delivery to maximize impact. For instance, a spoofed DNS response might redirect users to a site that automatically downloads malicious software onto their device.
Another important factor is timing. Attackers must deliver forged DNS responses faster than legitimate servers to ensure their malicious data is cached. This race condition is a key element of DNS spoofing attacks and highlights why speed and precision are critical to their success.
History of DNS Spoofing
DNS spoofing has its roots in the early days of the internet, with the first documented attacks emerging in the late 1990s. The attack became more sophisticated over time, particularly after the Kaminsky vulnerability was revealed in 2008. This flaw highlighted systemic weaknesses in DNS protocol, prompting widespread security upgrades.
| Year | Event | Impact |
|---|---|---|
| 1997 | Early DNS spoofing incidents | Highlighted DNS vulnerabilities |
| 2008 | Kaminsky vulnerability discovery | Exposed systemic DNS protocol weaknesses |
| 2010s | Rise of advanced DNS spoofing techniques | Increased adoption of DNSSEC |
Following the Kaminsky disclosure, organizations began implementing stronger protections such as randomizing DNS queries and adopting DNSSEC (Domain Name System Security Extensions). These improvements significantly reduced the likelihood of successful spoofing attacks, but they did not eliminate the threat entirely.
In recent years, attackers have shifted their focus toward more complex attack chains, combining DNS spoofing with social engineering and advanced malware. This evolution demonstrates that while defenses have improved, attackers continue to adapt and find new ways to exploit DNS-related weaknesses.
Types of DNS Spoofing
| Type | Description |
|---|---|
| DNS Cache Poisoning | Attackers corrupt the cache of DNS resolvers, leading to malicious redirections |
| Man-in-the-Middle | Attackers intercept and alter DNS communications between users and servers |
| Domain Hijacking | Entire domains are redirected to unauthorized servers |
Each type presents unique risks. Cache poisoning can affect large numbers of users at once, while man-in-the-middle attacks are often more targeted and difficult to detect. Domain hijacking, on the other hand, can completely take over a legitimate website’s traffic, causing severe reputational and financial damage.
How Does DNS Spoofing Work?
DNS spoofing exploits the inherent trust in the DNS hierarchy. By sending forged responses faster than the legitimate DNS server, attackers deceive the system into caching false data. This misinformation remains in the cache until it expires or is manually corrected.
In many cases, users remain unaware that anything is wrong. The browser may still display the expected domain name, and the fake website may appear visually identical to the real one. This makes DNS spoofing particularly effective for credential harvesting and financial fraud.
To counter this, modern systems rely on encryption and validation mechanisms such as DNSSEC, HTTPS, and secure DNS resolvers. These technologies help verify that DNS responses are authentic and have not been tampered with during transmission.
Pros & Cons of DNS Spoofing
| Pros (For Attackers) | Cons (For Users/Organizations) |
|---|---|
| Easy to execute on vulnerable systems | Compromises sensitive user data |
| Enables phishing and malware distribution | Disrupts trust in internet infrastructure |
| Can be used for espionage or large-scale attacks | Requires time and effort to detect and mitigate |
Despite its effectiveness for attackers, DNS spoofing often leaves traces that can be detected through monitoring tools and anomaly detection systems. Organizations that invest in visibility and logging can identify unusual DNS behavior and respond before significant damage occurs.
Applications or Uses
Industry-Specific Applications
Finance: Preventing phishing attacks targeting online banking platforms.
E-commerce: Protecting customer transactions from interception.
Healthcare: Securing patient data on medical portals.
Government: Safeguarding classified communications from espionage.
General Use Cases
Threat Intelligence: Its insights help organizations prepare defenses.
Education: Raising awareness about DNS vulnerabilities among users.
Policy Making: Driving standards for secure DNS protocols, like DNSSEC.
Beyond these uses, DNS spoofing awareness also helps organizations improve their overall security posture. By understanding how attackers exploit DNS, businesses can implement stronger validation processes, train employees to recognize suspicious behavior, and adopt technologies that reduce reliance on unverified data sources.
Resources
- Cloudflare. What Is DNS Cache Poisoning?
- Imperva. DNS Spoofing Explained.
- Panda Security. DNS Spoofing: What You Need to Know.
- Proofpoint. DNS Spoofing Reference Guide.
- UpGuard. Understanding DNS Cache Poisoning.
