Zero Trust Network Access Materials or Tools Needed
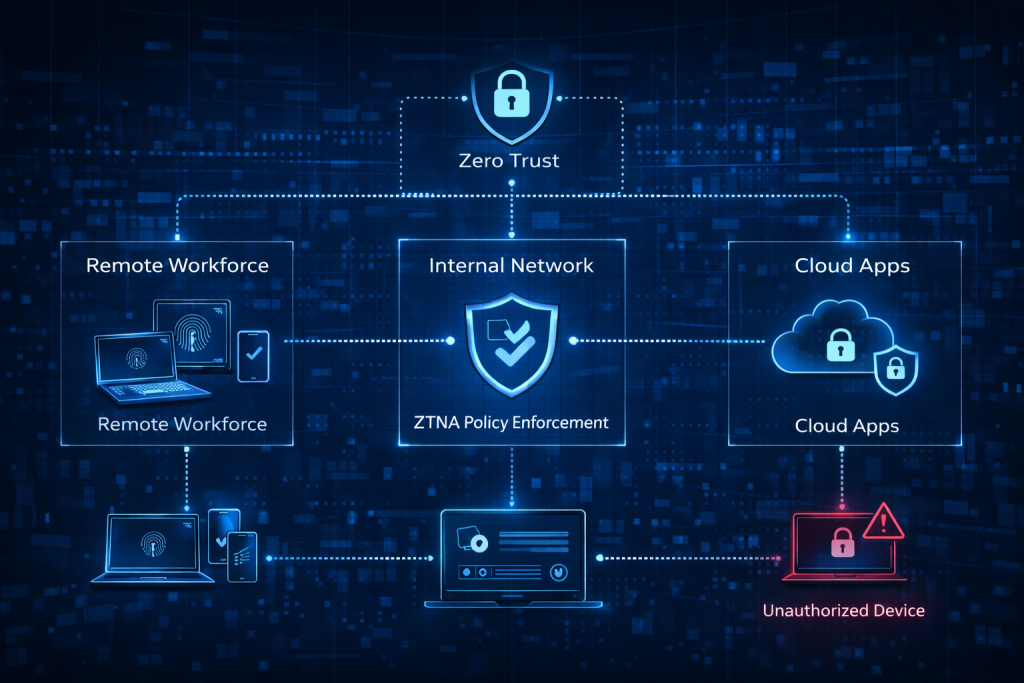
To implement Zero Trust Network Access successfully, you need more than good intentions. You need visibility, control, and tools that help enforce verification at every step. Think of it like building a secure checkpoint system rather than leaving every hallway open. A strong Zero Trust Network Access strategy usually begins with identity tools, access controls, endpoint protection, and monitoring systems that work together.
In real-world environments, teams often discover that the challenge is not a lack of technology, but a lack of alignment. One team uses one platform, another uses something else, and no one has a complete picture. That is why Zero Trust Network Access works best when your tools are connected and your policies are clear.
| Tool or Material | Purpose |
|---|---|
| Identity and Access Management (IAM) | Verifies users and controls permissions |
| Multi-Factor Authentication (MFA) | Adds extra identity checks before access is granted |
| Network segmentation tools | Limits movement across systems |
| Endpoint security solutions | Protects laptops, phones, and other endpoints |
| Monitoring and logging tools | Tracks access attempts and suspicious activity |
| Cloud platform integrations | Extends Zero Trust Network Access across hybrid environments |
| Policy engine or access controller | Applies least-privilege rules consistently |
Zero Trust Network Access Instructions
Step 1

Start by assessing your current environment before you enforce Zero Trust Network Access. Map out your users, devices, applications, data stores, and access pathways. This step sounds basic, but it is often the moment teams realize just how many hidden dependencies exist. I have seen environments where an old service account still had access to sensitive systems long after the original project was gone. Zero Trust Network Access depends on clarity, so you need to know exactly who is accessing what, from where, and why. Once you identify critical assets, rank them by business importance and security risk so you can protect the most valuable areas first.
Step 2
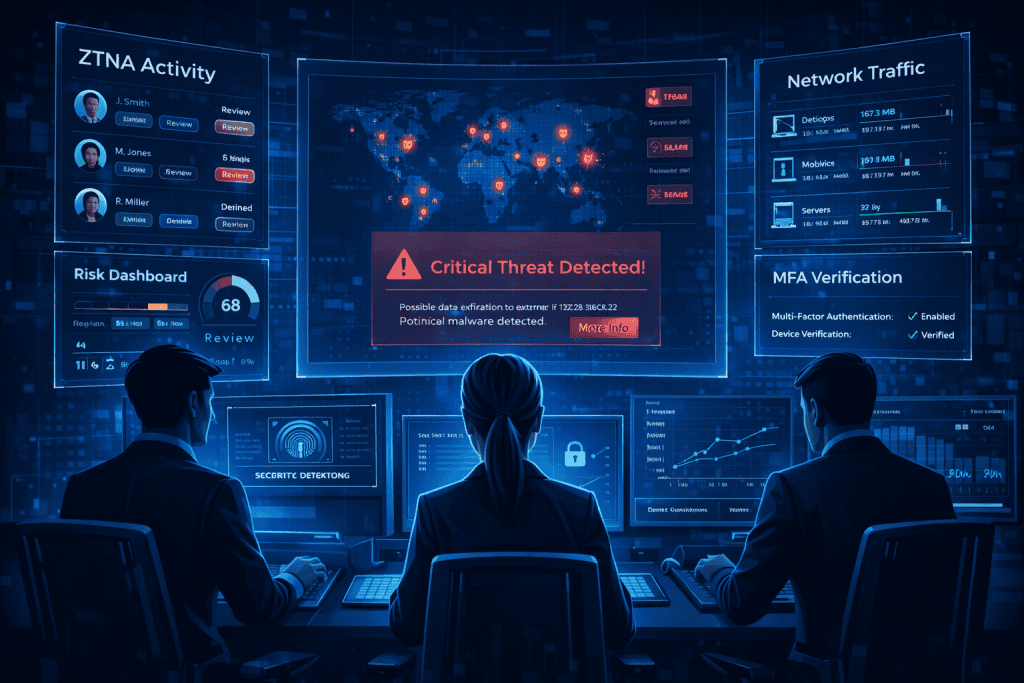
Implement strict identity verification across the organization. At the heart of Zero Trust Network Access is the principle of “never trust, always verify.” Every login request should be treated as if it comes from an untrusted source until proven otherwise. Use MFA, single sign-on, conditional access, and strong identity checks to confirm that users and devices are legitimate. This is where many organizations get their first quick win. When credentials are stolen, weak login protection becomes an open door. By contrast, Zero Trust Network Access forces attackers to clear multiple barriers instead of one. That shift alone can dramatically reduce unauthorized access.
Step 3
Apply segmentation and least-privilege access rules. A strong Zero Trust Network Access model does not give employees or systems broad visibility just because they are already “inside.” Instead, it limits access to only what is necessary for a specific task. Create micro-perimeters around critical assets so one compromised account does not expose the entire network. This step is especially valuable in environments with cloud services, contractors, and mixed device types. It is also where advanced technology can make policy enforcement easier. Proper segmentation shrinks your attack surface and keeps threats from moving sideways through your environment.
Step 4
Deploy continuous monitoring and threat detection. Zero Trust Network Access is not a one-time setup; it is an ongoing discipline. Once access is granted, your systems should keep watching. Logging tools, SIEM platforms, and anomaly detection systems help identify unusual activity, such as impossible travel logins, repeated failed access attempts, or device behavior that suddenly changes. In practice, this constant visibility gives teams a fighting chance. Without it, suspicious behavior can hide in plain sight. A mature Zero Trust Network Access environment continuously checks, records, and evaluates activity so you can detect threats before they become incidents.
Step 5
Test, refine, and educate users. This is the part many teams underestimate. Zero Trust Network Access can fail if employees do not understand why access rules changed or how to work within them. Train users on secure login habits, phishing awareness, and device hygiene. Review policies regularly to make sure they still reflect business needs. New hires, mergers, remote teams, and fresh applications all change the access picture. The best Zero Trust Network Access deployments evolve with the organization. In a world full of new inventions and shifting digital workflows, security policies need to stay just as flexible as the business itself.
Zero Trust Network Access Tips and Warnings
A smart Zero Trust Network Access rollout is steady, intentional, and realistic. Do not try to rebuild everything at once. Start with your highest-value systems, then expand in stages. Many organizations make the mistake of chasing perfection on day one, which usually leads to stalled projects and frustrated users. Instead, treat Zero Trust Network Access like a long-term operating model. Build it layer by layer.
One helpful tip is to prioritize user experience alongside security. If your controls are too confusing, staff will look for shortcuts. Another tip is to review third-party access just as carefully as employee access. Vendors, consultants, and unmanaged devices can become weak points if overlooked. With more cloud services, mobile work, and iot devices entering business environments, those blind spots add up quickly.
Be careful not to assume internal traffic is safe. That old assumption is exactly what Zero Trust Network Access is designed to challenge. Also, do not overlook training. Even the best controls can be undermined by a rushed click, weak password habits, or poor awareness. In a landscape filled with Innovation, futuristic technology, and rapidly changing threats, education remains one of the strongest defenses. A reliable website security strategy becomes much stronger when Zero Trust Network Access is supported by people who understand it.
| Tip or Warning | Why It Matters |
|---|---|
| Start with critical assets | Reduces risk faster and makes rollout manageable |
| Enforce MFA everywhere possible | Stops many credential-based attacks early |
| Avoid over-permissioning users | Limits damage if one account is compromised |
| Monitor continuously | Helps catch abnormal behavior in real time |
| Train users regularly | Reduces human error and social engineering risk |
| Review policies often | Keeps Zero Trust Network Access aligned with business changes |
Conclusion
At its core, Zero Trust Network Access is about discipline, visibility, and smart control. The key steps are simple in theory: understand your environment, verify every identity, limit access, monitor activity, and keep improving. In practice, these steps create a much stronger security posture for modern organizations.
If you are planning to strengthen cybersecurity in a cloud-first, remote-friendly world, Zero Trust Network Access is a practical place to begin. Start small, stay consistent, and build confidence one protected asset at a time. The effort pays off in resilience, trust, and peace of mind.
FAQ
What is the core principle of Zero Trust Network Access?
Zero Trust operates on the principle of “never trust, always verify.” This means no device, user, or system is trusted by default, even if they are within the network.
How does Zero Trust differ from traditional security models?
Unlike traditional security models that rely on perimeter defenses (like firewalls), Zero Trust assumes that threats can come from both inside and outside the network, requiring strict identity verification and access control at all times.
Can Zero Trust Network Access be implemented in the cloud?
Yes, Zero Trust is highly compatible with cloud environments. In fact, many cloud service providers offer built-in tools that support Zero Trust principles, such as IAM and monitoring solutions.
Resources
- Tigera. Guide to Zero Trust Architecture.
- Zscaler. How to Implement Zero Trust.
- Cato Networks. Zero Trust Network Access.
- StrongDM. How to Implement Zero Trust.
- Palo Alto Networks. What is Zero Trust Architecture.
