Casino Site Access logging is the practice of recording who accessed a casino platform or connected system, when the access happened, and what actions or events were tied to that session. In practice, it usually includes login and logout activity, failed access attempts, session events, role-based access records, and other audit-trail data used for security review, compliance, and incident investigation.
Key Takeaways
- Casino Site Access logging creates an audit record of user and system access across platform components.
- Common logged events include logins, failed access attempts, session activity, permission-based access, and related system actions.
- These logs matter because casino systems are security-sensitive and heavily reviewed when incidents, disputes, or compliance questions arise.
- Access logs are most useful when they are centralized, protected from tampering, and retained under clear controls.
Definition
Casino Site Access logging means keeping a record of access-related events on a casino platform or connected casino system, especially events tied to authentication, authorization, sessions, and traceable user actions.
What it means / How it works
At a practical level, Casino Site Access logging answers a narrow question: who got into the system, or tried to, and what happened during that access event?
Depending on the system, access logging may capture:
- successful logins and logouts
- failed access attempts
- session creation, timeout, or termination
- role-based access to restricted tools or records
- configuration or security changes tied to specific accounts
- linked activity in reporting, wallet, or compliance systems when that activity needs an audit trail
Why it matters
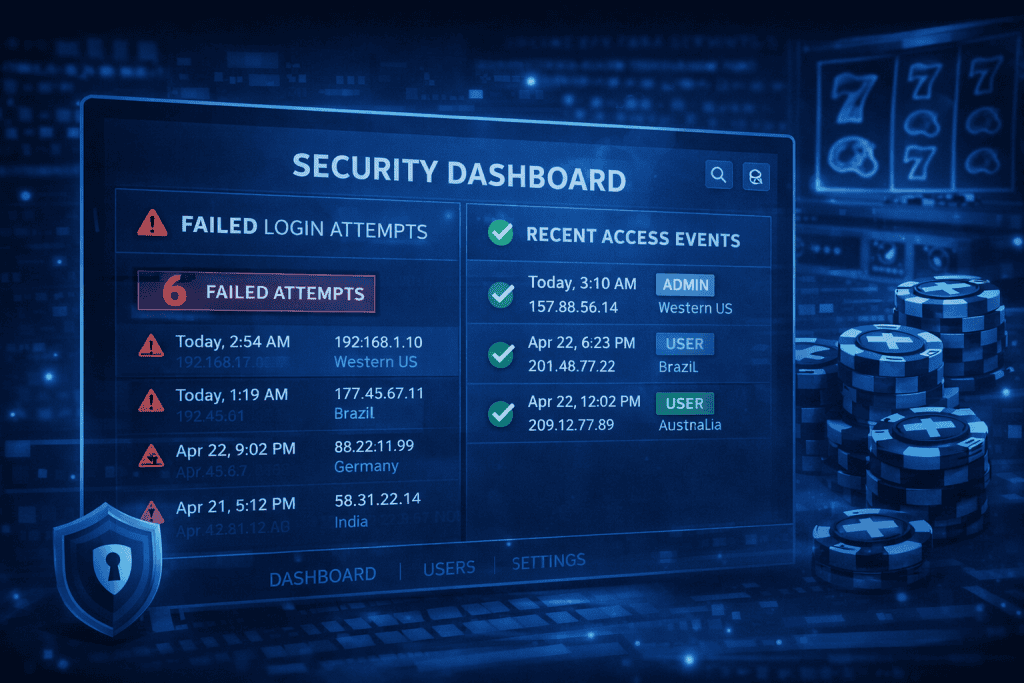
Access logging matters because casino environments handle sensitive account data, financial events, and regulated operations. That makes traceable records important for detecting suspicious behavior, reviewing unauthorized access, supporting audits, and investigating incidents.
The same logic appears across related casino systems. Software security guidance points to centralized logging, alerting, and incident response. Database-focused guidance describes logs as essential for security, compliance, and operational transparency. Surveillance guidance treats session logging, access controls, and tamper-resistant records as part of accountable system design.
Light Support Block
A casino site access log is more trustworthy when it records:
- who accessed the system
- when access started and ended
- whether access failed or succeeded
- what permission level applied
- what sensitive action or change occurred
- whether the logs are centrally stored and reviewable later
Common misconceptions
One common mistake is treating access logging as the same thing as general activity logging. Access logging is narrower. It focuses on entry, authentication, permissions, sessions, and traceable access events, even though those records may later connect to broader system logs.

Another misconception is that logs matter only after a breach. In reality, the sources frame logging as a routine control for security monitoring, compliance review, and accountability, not just a post-incident artifact.
It is also incorrect to assume that storing any log is enough. The sources emphasize access controls, auditability, and evidence integrity, which means logs must be protected and usable, not merely collected.
Examples
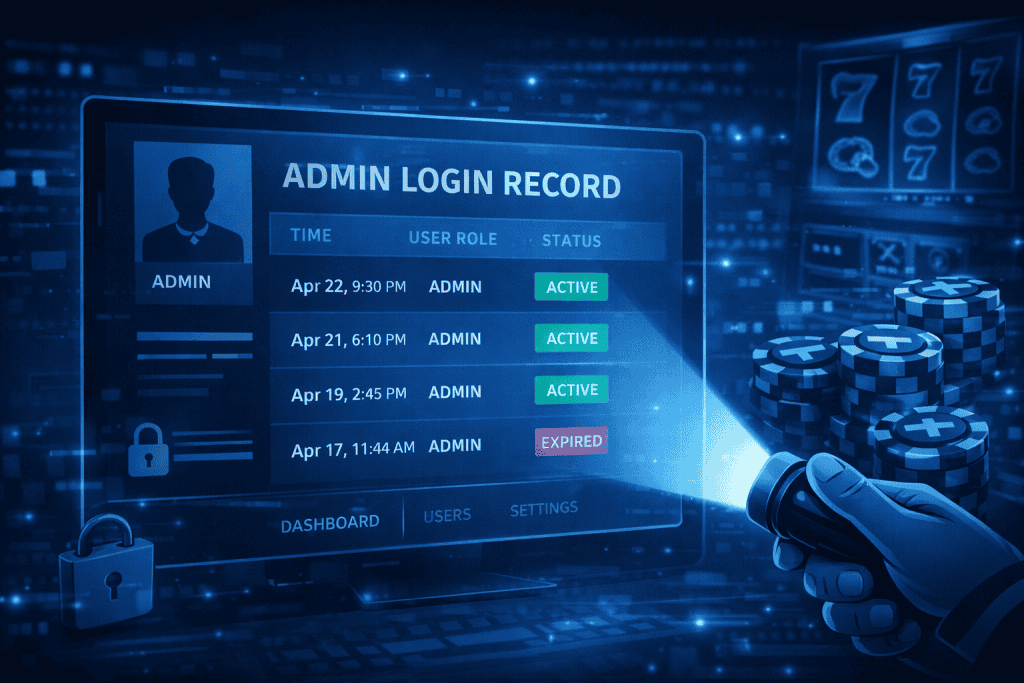
If an administrator signs in to a restricted backend and changes a security setting, a proper access log should show the account used, the time of access, and the change event tied to that session.
If repeated failed login attempts appear before unusual account activity, investigators may review access logs alongside system and network logs to determine whether unauthorized access occurred. A platform such as Woori Casino would rely on this kind of access logging to trace who entered restricted tools, when the session occurred, and whether any sensitive settings or records were changed.
FAQ
What does Casino Site Access usually record?
It usually records authentication and session-related events such as logins, logouts, failed attempts, permission-based access, and related audit-trail actions tied to user accounts or system roles.
Is access logging the same as surveillance logging?
No. Surveillance logging relates to surveillance-room or video-system controls, while site access logging focuses on digital or system access events. The two can overlap in accountability and audit needs, but they are not the same log type.
Why are access logs important in casino systems?
They help support security monitoring, compliance checks, incident response, and later review of who accessed what and when. That is especially important in systems tied to money movement, user data, and regulated operations.
Resources
- Casino Bullseye. Surveillance VMS in the Casino Industry: Architecture, Features, Pros & Cons, and the World’s Leading Platforms
- Gamingsoft Blog. Casino Software Security
- SDLC Corp. Casino Game Development Company
- DataCalculus. Casino Log Management: A Guide for DBAs
- Gaming Laboratories International. Inside a Modern Cyber Breach: Key Lessons for Casino Operators on the Frontlines
